- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
SECURITY USE CASE
Challenges
Advanced cyberattackers know how to exploit what you rely on to succeed: access to data, trusted software, and people to get the job done. Once inside, these malicious actors know how to wreak havoc in your network. They move laterally and use encryption to cover their tracks so they can accomplish their real objective, executing ransomware or exfiltrating your valuable customer data and intellectual property. They can cut off access to the critical systems and data you need, all while eroding trust among your customers and your team. Eliminating blind spots and responding to threats in their earliest stages is critical to prevent business disruption and minimize financial impact.
Opportunities
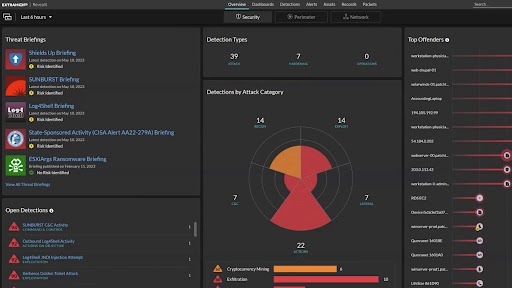
RevealX discovers and classifies all devices on the network, then analyzes the transactions between them. Even SSL/TLS-encrypted traffic is no match for the 90+ enterprise protocols RevealX can decode at up to 100 Gbps. Along with dramatically speeding up detection so you can reduce dwell time of threats in your environment, RevealX provides one-click investigations for each detection.
The vulnerabilities of your software supply chain are hard to identify because you can rarely access your suppliers’ code. Zero day and unpatched vulnerabilities are leaving gaping holes in your security posture. By monitoring your network traffic, RevealX can detect when an attacker has penetrated your network through your software supply chain and catch attackers before they do any significant damage.

See It in Action
Solution
Leverage the network as a central source of truth in order to stop cyberattacks. The ExtraHop RevealX platform allows you to get unparalleled visibility and security control across all assets in your organization.
Security
Use the power of network visibility and AI for real-time detection, rapid investigation, and intelligent response for any threat.