- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Registry modification is associated with a persistent, planned attack rather than a random, opportunistic attack. If the attacker can remotely modify the registry, they can launch additional attacks, disable security tools, run arbitrary code, or delete event logs.
Category
Decryptions
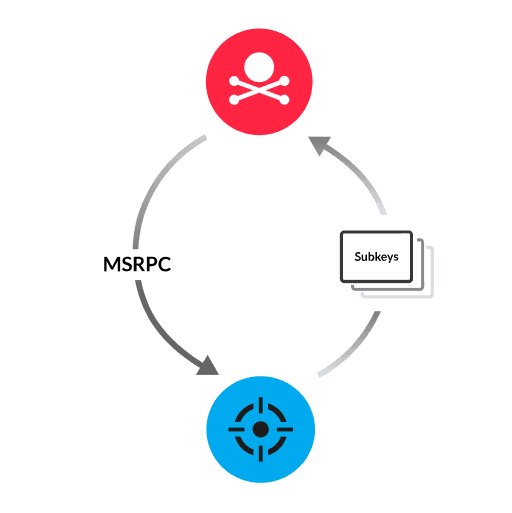
Every Windows device has a registry, which is a built-in hierarchical database that contains configuration data in the form of key-value pairs. This configuration data controls a number of critical processes, such as scripts that run at startup, initialization of security tools, and event logging. To change certain key values remotely, the attacker needs administrator privileges and access to the Remote Registry service on the target device. The attacker sends a Microsoft remote procedure call (MS-RPC) with commands to modify values of a specified key value. For example, the attacker can replace the value for the HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit key, which specifies scripts that run during system initiation. The new value includes the original string, but adds a path to malicious code.
Prevent unauthorized users from accessing the Windows registry by limiting the number of users with local administrator privileges
Restrict registry key from being accessed over a network connection
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
