- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
The SharpDPAPI attack tool is publicly available, but an attacker must have local administrator privileges, knowledge of Active Directory (AD), and a Data Protection API (DPAPI) backup key, which decrypts the obtained data. A successful exploit can lead to stolen data and further attacks on your network.
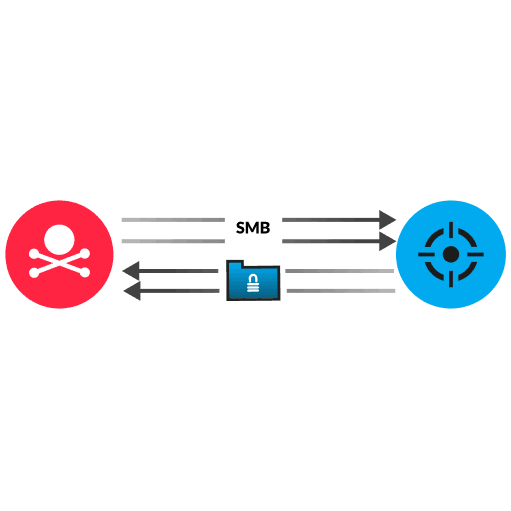
Category
The DPAPI is built into Windows operating systems and enables fast encryption of sensitive data. An attacker with administrator access runs the SharpDPAPI triage command locally, directing the command to remotely retrieve encrypted DPAPI files from the victim device by authenticating a user session over the SMB protocol. The triage command performs bulk data extraction by automatically running several smaller SharpDPAPI commands that enumerate multiple common storage locations such as the Windows Credential Manager, Windows Vaults, Remote Desktop Connection Manager, and certificates. For each found file, it sends an SMB CREATE request to remotely access the existing binary data from the file. After a successful exploit, the attacker leverages the stolen backup key to decrypt the masterkey for the victim. This step enables the attacker to access the entire set of DPAPI-protected credentials and secrets.
Enforce strong network segmentation and user authentication policies
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
