- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
AsyncRAT and AsyncRAT variants are open-source malware that are easily accessible to attackers. This malware infects systems through user interaction, such as clicking phishing links or malicious ads. After a device is compromised, an attacker can remotely control the device, move laterally, or deploy secondary payloads and exfiltrate sensitive business information from the victim.
Category
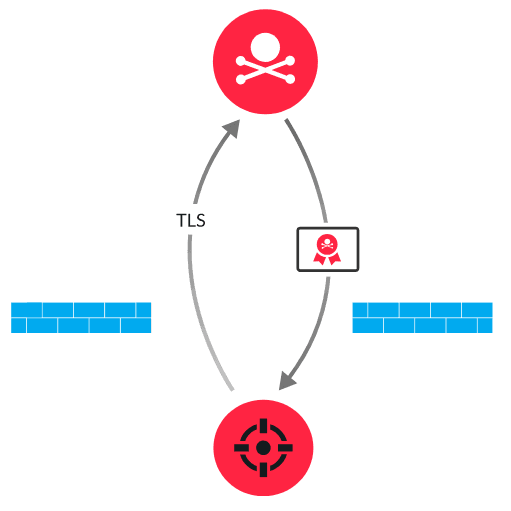
AsyncRAT variants include DcRAT, XiebroRAT, SantaRAT, and VenomRAT. These tools establish a secure C&C channel from a victim device by initiating a TLS connection to an attacker-controlled server. During the session negotiation, the C&C server presents a certificate with hardcoded parameters that identify the traffic associated with AsyncRAT or variants. By establishing a successful encrypted session, the attacker can remotely perform malicious activities, including credential theft, file exfiltration, keylogging, and screen capturing.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
Visit this resource for more information
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
