- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
SECURITY Use Case
Challenges
In a Zero Trust architecture, every device, user, and packet is a potential threat. You cannot rely on logs that can be altered or agents that can be bypassed. To achieve true visibility, you must look to the network because it is the only place where attackers have nowhere to hide.
Zero Trust is a rigorous framework of continuous verification requiring data that doesn't lie. By treating the network as your foundational source of truth, you gain the empirical evidence needed to validate identity, audit compliance in real time, and expose compromise when authenticated entities act like adversaries.
By analyzing raw network traffic, network detection and response (NDR) provides the continuous monitoring and policy validation required to turn Zero Trust into an operational reality.

Datasheet
Learn about the rise of Zero Trust, the challenges of these mandates, and how RevealX transforms the framework from an abstract concept into an operational reality.
Opportunities
ExtraHop RevealX provides the NDR capabilities essential for Zero Trust through continuous, high-fidelity monitoring of the critical east-west corridor. By transforming raw traffic into ground truth, RevealX ensures your implementation relies on actual behavior rather than static credentials. This enables granular control and neutralizes lateral threats before they can scale.

BLOG
Zero Trust replaces perimeter models. Discover implementation barriers and learn how network ground truth transforms this strategy into reality.
See it in action
This walkthrough shows how ExtraHop closes the critical security visibility gap that exists in modern SSE (Security Service Edge) architectures. We achieve this by integrating with Zscaler Private Access (ZPA) to provide deeper visibility and stronger Zero Trust across your environment.
Solution
Secure and optimize critical assets across hybrid and cloud environments with RevealX. By analyzing raw traffic, NDR provides the continuous monitoring and policy validation required to turn Zero Trust into operational reality.
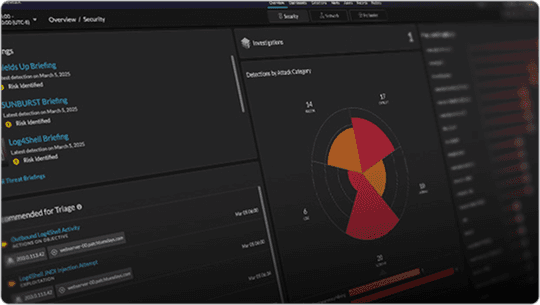
Security
Use the power of network visibility and AI for real-time detection, rapid investigation, and intelligent response for any threat.