- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
It is common for attackers to establish command-and-control (C&C) channels after the initial device compromise. The presence of a C&C channel on your network indicates that an attacker might be conducting a persistent attack. The ultimate objective of a persistent attack, such as data exfiltration, could have a significant impact on a business or organization.
The system might change the risk score for this detection.
Category
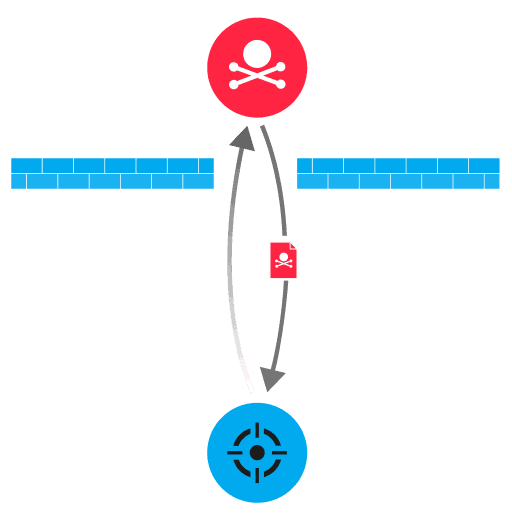
Attackers can remotely interact with the command-line interface of a compromised device through a shell program or network utility, which enables the attacker to send commands over a TCP connection. The commands can be encrypted or tunneled through other protocols to help the attacker evade detection. After running commands, the attacker can ultimately control the remote device and then pivot to compromise other devices on the network.
Because IT administrators often remotely manage devices through a shell, investigate to confirm the shell activity is legitimate.
Configure firewalls to block outbound traffic to suspicious external hosts
Remove or prohibit unnecessary network utilities that enable users to easily create shells for most programming languages
Provision devices to communicate over authorized interfaces
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
