- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Remote access software is a common target for attackers because of their prevalence in enterprise environments and they provide remote access to internal network devices. If an attacker collects system credentials, they can remotely control the desktop on the victim and potentially establish a command-and-control (C&C) channel.
The system might change the risk score for this detection.
Category
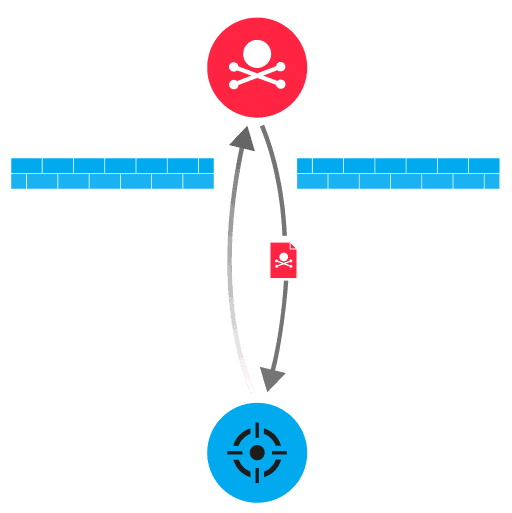
Remote access software such as TeamViewer and remote service protocols such as the Remote Desktop Protocol (RDP), enable users to interact with the graphical user interface (GUI) of a device from a remote location. Attackers can remotely access devices after obtaining user credentials through phishing, device compromise, or brute force techniques. After connecting to the internal device, the attacker can establish a persistent presence, create an interactive C&C channel, or connect to other target systems within the network.
IT administrators often remotely interact with internal enterprise resources through remote desktop services. This legitimate activity can appear similar to malicious interactive remote desktop sessions.
Configure firewalls to block common remote service protocols, such as VNC (RFB) and RDP, to unknown external hosts
Disable or remove unnecessary desktop sharing software
Enforce multi-factor authentication for remote logins
Determine if any user credentials have been compromised for an unauthorized remote desktop connection
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
