- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Enumeration is a simple but important step taken by attackers after an initial network compromise. Seatbelt is a tool that makes enumeration relatively easy to perform, but an attacker needs network access to the target remote device and credentials to run Seatbelt. Enumeration activity typically does not negatively affect network performance, but attackers can leverage this information to find new targets in an attack campaign.
Category
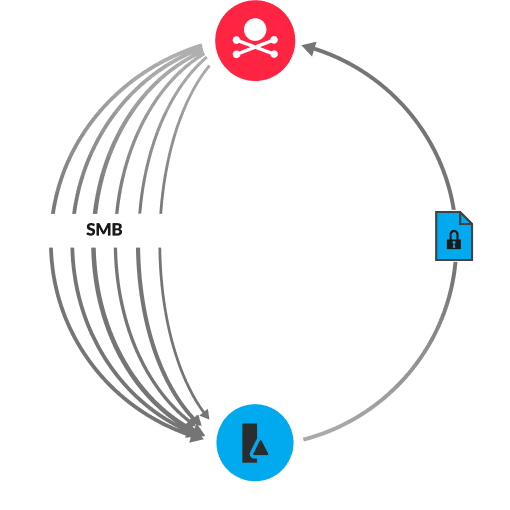
Seatbelt is a tool for running security checks on local and remote Windows devices, but this tool can also enumerate valuable information for an attacker. Seatbelt can automatically run the CloudCredential module, which finds authentication information for cloud services such as AWS, Google Cloud, and Azure. A successful command can lead to stolen credentials and further attacks on the network.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
