- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Creating a process by running a Windows Management Instrumentation (WMI) method requires local administrator privileges, which can be difficult for attackers to acquire. But a successful attacker can leverage applications, many preinstalled on Windows devices, to interact with WMI and achieve attack campaign objectives such as lateral movement. The severity of the attack depends on which devices are compromised and the type of commands that are run.
The risk score can be adjusted for this detection.
Category
Decryptions
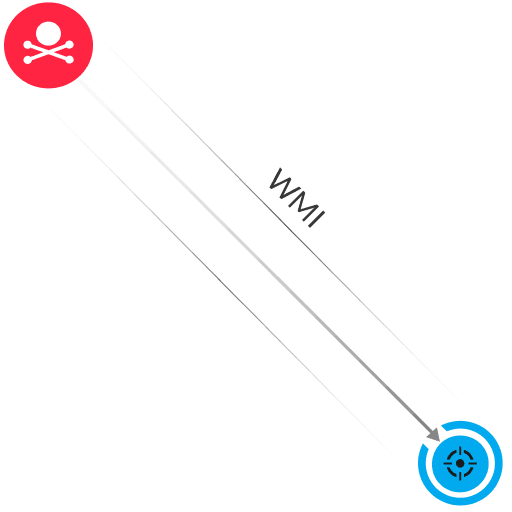
WMI is a set of specifications for Windows operating system components. Microsoft utilities and protocols can interact with WMI to perform actions on remote devices. For example, the WMI CreateProcess (also known as Win32_Process) method can start a process on a remote device to run commands. An attacker with local administrator privileges can interact with WMI by sending a Microsoft remote procedure call (MS-RPC) request to a remote device. The request includes the ExecMethod operation, which passes malicious commands to the WMI method on the remote device. As a result, the process is created and runs the malicious commands on the device.
Block or restrict WMI access to authorized IP addresses in Windows firewall settings
Limit the number of administrator accounts that have WMI privileges
Separate credentials for administrators by the type of remote activity
Restrict access to specific WMI namespaces to only relative administrative user accounts
Learn how attackers use the Impacket tool to move laterally in encrypted east-west traffic. Discover how ExtraHop RevealX provides the crucial visibility to detect these hidden threats.
WMI is a Microsoft-specific implementation of the Web-Based Enterprise Management (WBEM) standard. WMI allows you to gather information about and control various components of a Windows system.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
