- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Routers, WiFi extenders, and Internet of Things (IoT) devices with Realtek software development kit (SDK) firmware are sometimes exposed to the internet, but firmware implementation (and exploit mechanism) can vary by device. Public exploit code is available to exploit these vulnerabilities. An unauthenticated attacker can gain control of an IoT device, such as a router, to launch further attacks on a network.
Category
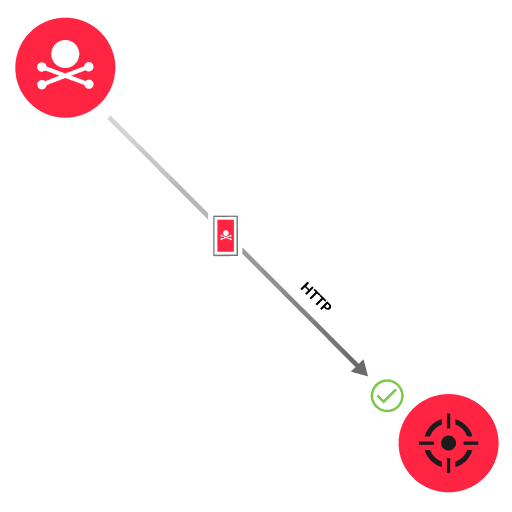
Realtek is a semiconductor company that produces software development kit (SDK) firmware to enable wireless connections for various devices ranging from routers to IP cameras. Realtek SDK includes seven vulnerabilities (covered by CVE-2021-35395) that can lead to remote code execution (RCE). A majority of the vulnerabilities enable a buffer overflow in memory that can lead to RCE. The other vulnerabilities either allow command injection or unauthorized access to an interface that accepts system commands. To exploit these vulnerabilities, an attacker sends an HTTP request with a specially designed URI for a vulnerable path (such as /goform/formWsc). Depending on which vulnerability the attacker is exploiting, the HTTP request also includes a malicious payload or query parameters.
Quarantine the device while checking for indicators of compromise
Run regular software updates on IoT devices that rely on Realtek SDK firmware
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
