- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
An attacker with network access to an affected Windows 10 device can exploit this Microsoft Server Message Block 3.1.1 (SMBv3) vulnerability to acquire potentially sensitive information. Depending on the data accessed, the impact can be significant if important, proprietary, or customer data is disclosed.
Category
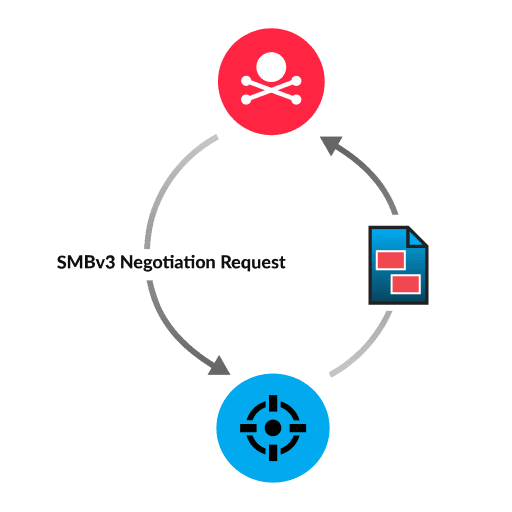
To exploit this SMB memory leak vulnerability, the attacker initiates a connection with a file server by sending a specially-designed SMBv3 packet. The SMB negotiation request from the attacker contains modified parameter values that allow uninitialized kernel memory to be stored in the response. As a result, the response from the server might disclose data that the attacker can leverage for future attacks.
This type of memory leak can occur in response to a legitimate SMBv3 negotiation request. Even if the request is from a legitimate source, the memory leak indicates that your environment is vulnerable to an attack and should be patched.
Install relevant patches for affected software and server versions
Restrict file share access to only authorized IP addresses and users
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
