Threat Briefing for AnyDesk Compromised Production Systems
Back to top
February 12, 2024
Threat Briefing for AnyDesk Compromised Production Systems
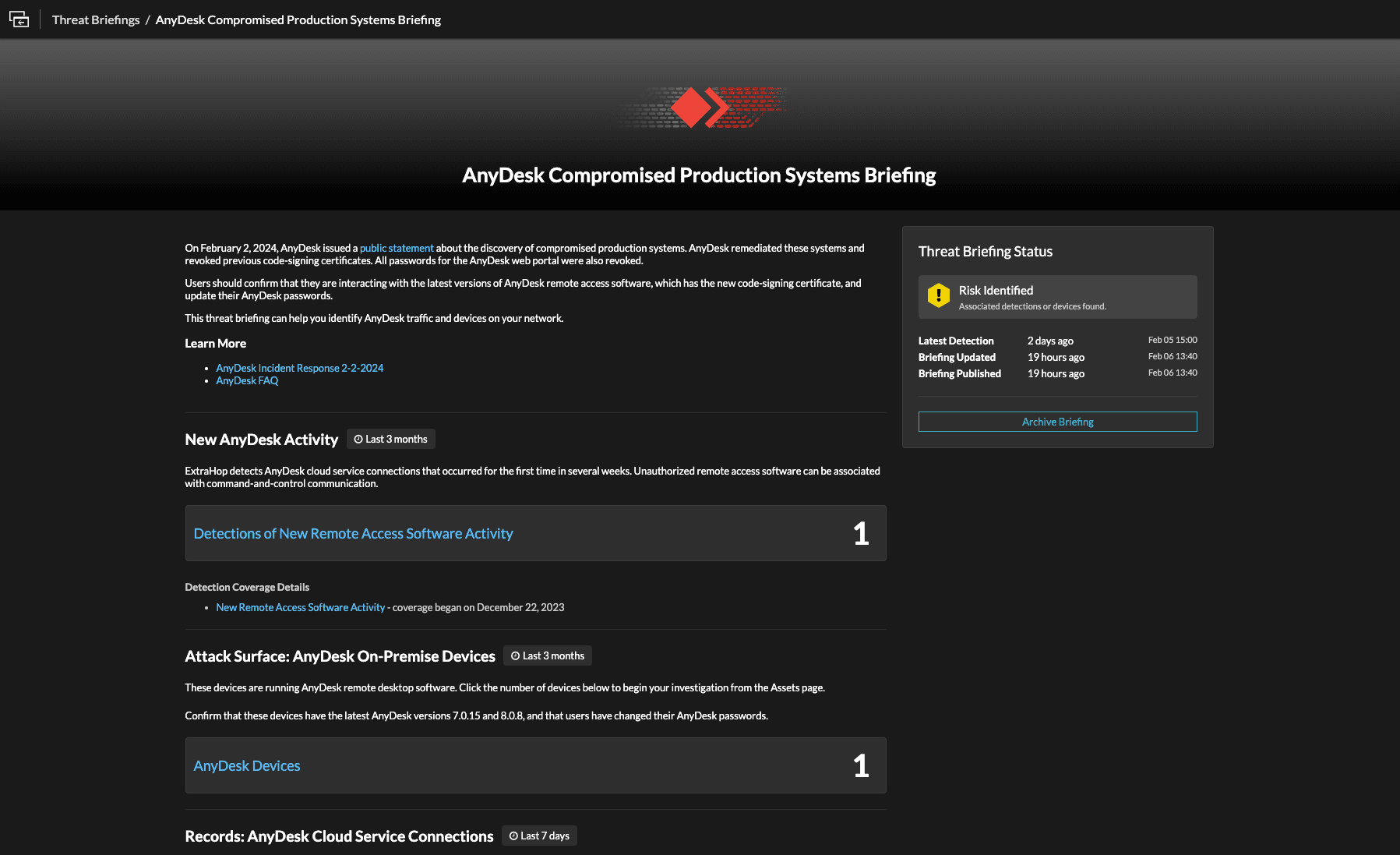
ExtraHop released a new Threat Briefing for AnyDesk Compromised Production Systems in its RevealX network detection and response (NDR) platform.
This latest Threat Briefing introduces a new detection, a preconfigured device query, and a preconfigured records query. RevealX now detects AnyDesk cloud service connections that occurred for the first time in several weeks.
The Threat Briefing for AnyDesk Compromised Production Systems in RevealX
AnyDesk Production Systems Compromise
On Feb 2, 2024 AnyDesk, a maker of remote desktop software, issued a public statement disclosing a security incident that showed evidence of a compromise in its production systems. AnyDesk remediated the affected systems and revoked all security-related and code signing certificates as well as web portal passwords. The company continues to advise customers to use the latest versions of AnyDesk (7.0.15 and 8.0.8) and to change their passwords if the same credentials are used elsewhere.
Remote Access Tools Are a Perennial Attacker Favorite
Because remote access software is widely used by IT teams to troubleshoot end-user computing issues, it’s a favorite target of threat actors. Leveraging remote access software means threat actors don’t need to use specialized malware, like remote access trojans, to establish command and control (C2) communication. Using legitimate software also allows threat actors to evade detection by antivirus, antimalware, and endpoint detection and response (EDR) tools.
Additionally, remote access software may allow malicious actors to bypass certain security policies and rules, and many remote access software applications–including AnyDesk–use end-to-end encryption, which can allow attackers to download malicious files that would ordinarily be blocked by a firewall without being detected. Further, remote access software can often be downloaded as portable executable files, which don’t need to be installed before they launch and often don’t require administrator privileges to run. They can then be used to run other software that ordinarily would be blocked by software management policies.
Inside the RevealX Threat Briefing for AnyDesk
While there’s no evidence according to AnyDesk that end user devices have been affected by the compromise or that any customer data has been stolen to date, the new Threat Briefing in RevealX provides AnyDesk users with an additional security control.
The preconfigured device query allows customers to identify any devices running AnyDesk remote desktop software. The records query allows customers to view all transactions that have connections to the AnyDesk cloud service. Together, the device and records query provide customers a starting point to confirm these devices have the latest AnyDesk versions (7.0.15 and 8.0.8) and that users have changed their AnyDesk passwords.
ExtraHop is invested in identifying remote access services and detecting new or anomalous usage of these services. In fact, even before we released the Threat Briefing for AnyDesk Compromised Production Systems, RevealX already had the ability to identify AnyDesk, enabling RevealX users to filter by devices running AnyDesk software and also track AnyDesk as a cloud service.

RevealX allows you to filter active devices by software, including AnyDesk.
Decryption and Behavioral Analytics Powered by Machine Learning Reveal Malicious Activity
The presence and use of remote access software on the network isn’t inherently suspicious. There are countless legitimate reasons for internal teams to use these tools. Threat actors are relying on this reasonable doubt to achieve their goals before security teams notice. But they aren’t counting on the network visibility RevealX provides.
What’s more, analytics powered by machine learning reveal every instance of remote access tools and shed light on unusual activity, like new connections to cloud services. With RevealX, organizations can quickly identify suspicious or unusual use of legitimate remote access software, like AnyDesk.

Software Architect
Ben Higgins is a Distinguished Software Engineer at ExtraHop with 15 years of experience in cybersecurity. He has extensive experience in systems engineering and protocol parsing, fingerprinting, and encryption. Ben is an experienced speaker, with recent appearances on Risky Business and Security Weekly. He holds a degree in Computer Science from the University of Washington.









