Identity Management Day 2026: Why Identity Providers are Ground Zero and What Defenders Can Do About It
Back to top
April 14, 2026
Identity Management Day 2026: Why Identity Providers are Ground Zero and What Defenders Can Do About It
Identity providers (IdPs) are primary targets for modern cyberattacks because they manage access for the entire enterprise. A single compromise can grant attackers access to the “keys of the kingdom”, often without triggering a single alert. This structural reality has allowed attackers to exploit identity-based vulnerabilities at an unprecedented scale.
This risk extends beyond human users, as the same platforms governing human identities are also being tasked with managing non-human identities (NHIs). Service accounts, OAuth tokens, and AI agents are multiplying faster than most organizations can track, emerging as significant “insider” threats, yet IdPs often have poor visibility into these accounts, an oversight creating blind spots that quietly persist until exploited.
The visibility gap exists because IdPs are built for authentication, not continuous, context-aware authorization. While they confirm identity at the point of login, they do not monitor what authenticated users do next. Consequently, suspicious network behavior often goes undetected long after access is granted. These gaps are further compounded by offboarding failures; when SaaS access is not de-provisioned, persistent backdoors allow former employees — or anyone with their credentials — to exfiltrate company assets long after their tenure ends.
Why Are Authentication Protocols Invisible to Most Security Tools?
Authentication protocols are invisible to most security tools because endpoint and log-based solutions cannot read encrypted authentication traffic. This limitation leaves gaps across every environment where that traffic flows.
The gaps mean that authentication-based attacks go unattributed. Analysts lack the identity context to determine who acted, on what system, or to what extent. The result is a detection void at the exact layer where credential abuse, token theft, and privilege escalation occur.
Without Protocol-Level Visibility and Decryption, How Far Can Attackers Go?
Attackers operating under stolen or abused identities often move laterally and escalate privileges for weeks before anyone notices. Token theft is a primary enabler. By stealing active session tokens, attackers bypass MFA entirely and impersonate legitimate users, and there are no indicators that conventional tools would flag.
Session hijacking extends this exposure when attackers reuse a stolen token from a different device, system, or location than the legitimate user — persisting and moving laterally even after MFA has been satisfied. To most conventional tools, the stolen token impersonating a privileged account looks like normal authenticated activity.
Non-human identities are particularly vulnerable to these unattributed attacks. NHIs often carry elevated access, generate little scrutiny, and have no human behavior baseline against which to detect anomalies — making them ideal footholds for long-term, undetected access.
What Do Protocol-Layer Visibility and Decryption Give Defenders That Other Tools Don’t?
Addressing these gaps requires real-time decryption and analysis of authentication traffic — the specific layer where token theft, credential abuse, and NHI anomalies actually occur. By exposing these encrypted flows, defenders gain three actionable capabilities that conventional tools simply cannot provide:
1. Token theft detection identifies and flags stolen authenticated sessions the moment they’re reused from a different device, location, or IP, giving analysts the information needed to contain an attack before lateral movement begins.
2. Active Directory (AD) attack detection of malicious activities that are hidden in encrypted AD protocols (LDAP, MSRPC, SMB, WSMAN).
3. Non-Human Identities (NHI) visibility by analyzing network traffic in real time and decrypting payloads, to ensure that encrypted channels used by these services do not hide malicious activity.
What Does It Take to Stop Identity Attacks Before They Become Incidents?
Identity providers are among the highest-value targets in the enterprise, and the attacks targeting them are engineered to evade the tools that most organizations rely on. Closing that gap requires visibility at the protocol layer — where authentication traffic flows, tokens are stolen, and identities are abused. To effectively detect and investigate these threats, analysts must have visibility not only into the user and associated devices, but also into their activity on the network as it relates to their access and privilege. That’s where ExtraHop excels. Through integrations with leading identity providers like Okta, Microsoft AD, and Entra ID, RevealX provides deep user enrichment, surfacing critical context, such as title, department, and now group memberships.
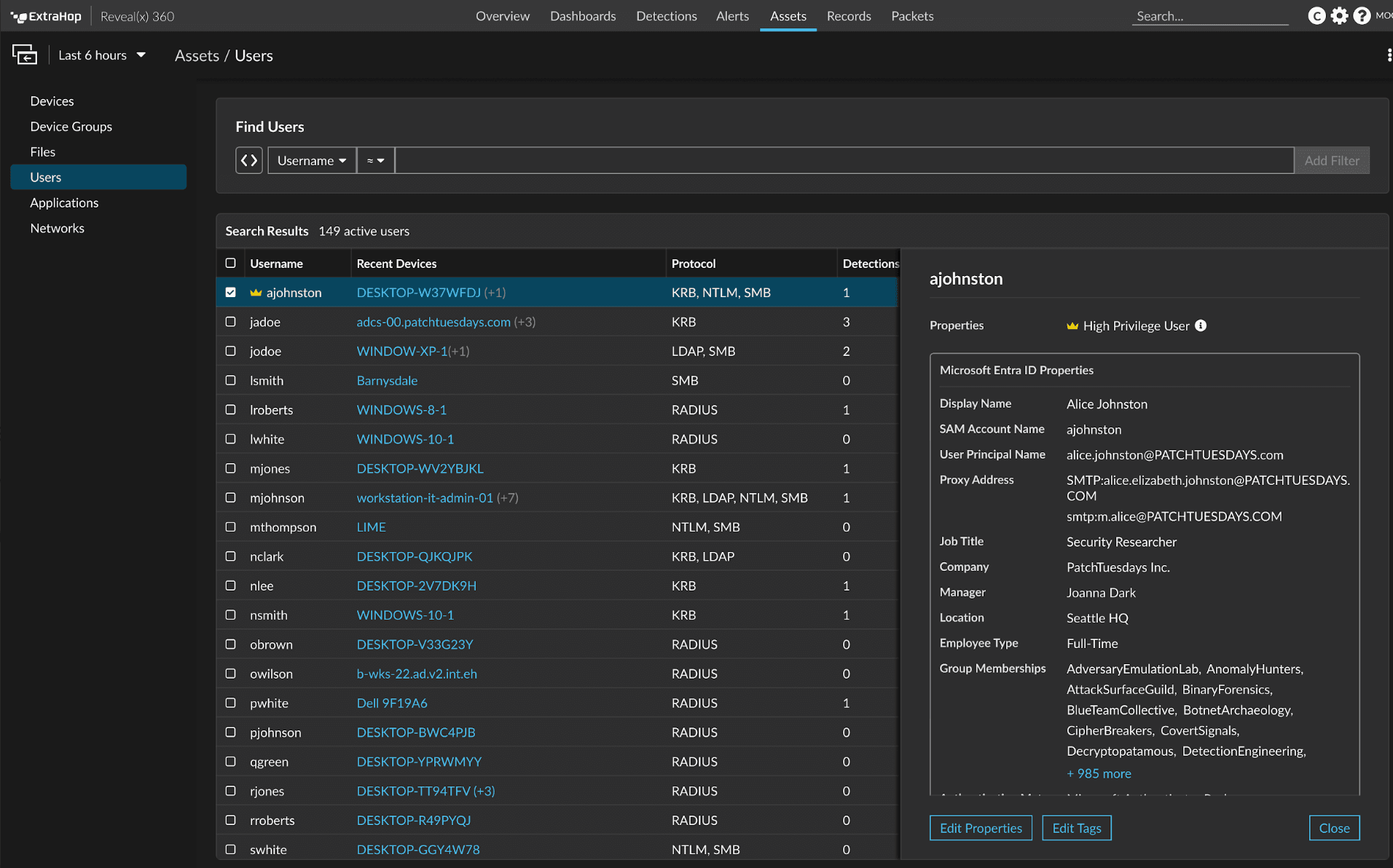
ExtraHop RevealX 26.2 delivers protocol-level visibility into the identity threats most tools miss, telling analysts precisely where to look, who is involved, their level of access, and exactly how much is at risk.
Learn more about how ExtraHop helps defeat identity attacks through our resource Arming Your SOC to Defeat Advanced Identity Attacks.

Senior Product Marketing Manager
Alexis is a Senior Product Marketing Manager at ExtraHop. She has been marketing cybersecurity and digital investigation products for the past 20 years focused on go-to-market strategy, new product launches, and content development.
Outside of work, Alexis enjoys volunteering for a teen mental health non-profit, traveling, and reading science fiction.
Follow Alexis on LinkedIn: https://www.linkedin.com/in/arobbins/









