- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
SECURITY USE CASE
How many ransomware threats are hiding on your network right now? It’s just one of many questions you should be asking now that threat actors have started switching up their tactics. With ExtraHop, every time attackers take a step in your network, you have an opportunity to regain the advantage—and catch them before the payload is activated.
Challenges
Credential compromise is now the dominant attack vector, with 81% of breaches involving compromised identities (Verizon DBIR Report). With a rise in SSO Federation, the increase in token theft, and prevalence of non-human identities, security teams need real-time identity insights to spot and investigate suspicious user behavior.
The conventional approach for ransomware mitigation focuses on the prevention of initial access and relies on backup recovery. Prevention alone is inefficient against ransomware: Attackers only need to succeed once, while you have to be right against them 100% of the time. And, restoring data doesn’t negate the downtime, the loss of business, reputation, and any legal consequences of a data breach.
Opportunities
ExtraHop reveals and stops ransomware campaigns coordinated by top threat actors, including Qilin, LockBit, and RansomHub, as they attempt to move laterally through your infrastructure, flipping the odds in your favor. Once inside your network, attackers have to constantly evade detection, but RevealX seeks them out and stops them. It spots unusual user activity and suspicious behaviors before data is encrypted. Guided investigative workflows help pinpoint impacted devices, and forensic visibility gets you to the root cause faster, ultimately reducing your mean time to remediation (MTTR).
Solution
With RevealX, detect threats other tools miss and fill coverage gaps left by EDR, SIEM, and logs. Gain the network intelligence you need with complete visibility, real-time detection, and rapid investigation.
Security
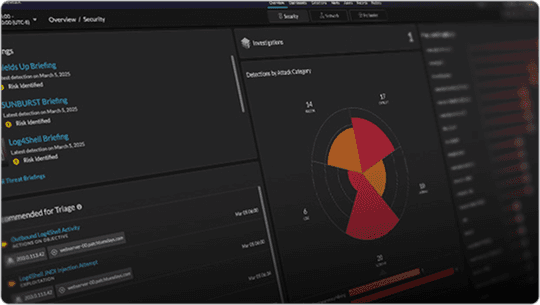
Investigate smarter, stop threats faster, and move at the speed of risk to reveal your cyber risk and build business resilience.

Ransomware attacks have evolved, and once inside, adversaries are moving laterally to accumulate valuable and sensitive data to ensure that organizations will pay a higher ransom. Intruders are now spending more time in your network, creating noise and causing them to risk detection. With RevealX, every time attackers take a step, you have an opportunity to regain the advantage—and stop them before they do more damage.