- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
An attacker with network access and stolen credentials is likely to run a scan to learn if they can gain privileged access to other devices. Attack tools can make this scan relatively easy to perform. This type of reconnaissance does not negatively affect network performance, but the attacker can identify new target devices that they can access.
The system might change the risk score for this detection.
Category
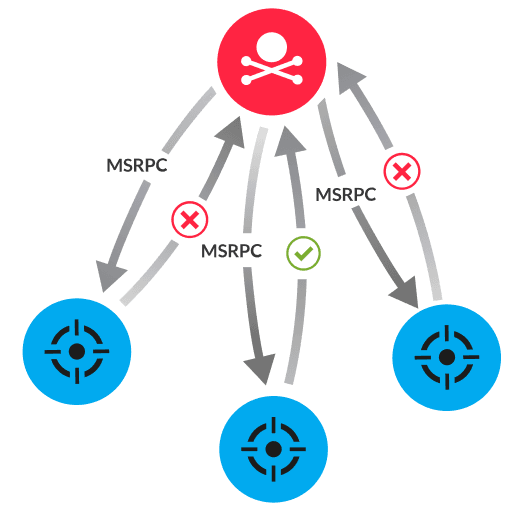
After stealing user credentials and infiltrating a network, an attacker runs a script that initiates SCM connection attempts across multiple devices simultaneously. Every Windows device has an SCM that enables administrators to remotely manage services. The script sends a Microsoft remote procedure call (MSRPC) to the SVCCTL interface. Next, the attacker analyzes the errors returned by each device and ignores devices that return ERROR_ACCESS_DENIED. Devices that allow the attacker to connect to the SCM are targeted for exploitation.
Implement network segmentation and the principle of least privilege to minimize the damage caused by a compromised device
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
