- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Enterprise software might run on high value, dedicated servers that only communicate with a specific set of protocols for routine tasks. If an attacker compromises a device, they might conduct malicious activity such as command-and-control communication, exfiltration, discovery, or reconnaissance over protocols that are unusual for that enterprise software. You should examine unusual protocol activity before it enables critical or costly attacks.
The system might change the risk score for this detection.
Category
An adversary can choose from many attack techniques to infiltrate a network, from performing supply chain attacks to exploiting unknown (zero-day) vulnerabilities. The ExtraHop Machine Learning Service can detect the stealthy attack behavior of a compromised device, regardless of exploit technique. When the ExtraHop system observes new, unusual protocol activity based on device history and behavior, the ExtraHop system then checks which enterprise software is running on the device. Examples of enterprise software include Microsoft Exchange Server, Apache HTTP Server, VMware vCenter, and JetBrains Teamcity. The ExtraHop system builds behavioral profiles for several types of enterprise software by analyzing protocol metadata over time and across many networks. New protocol activity is then compared to the behavioral profiles. If the new protocol activity is rarely associated with the enterprise software on the device, then the behavior is identified for further investigation.
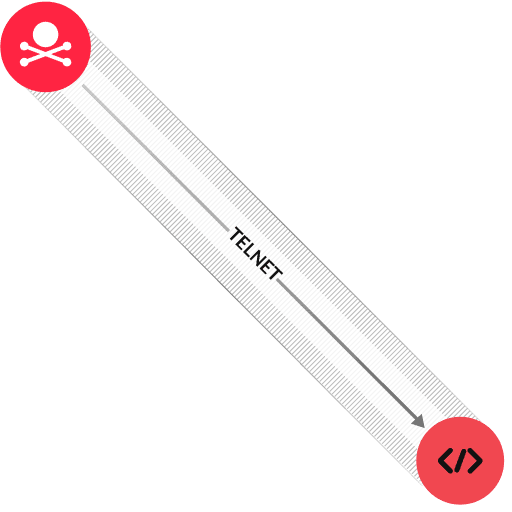
The diagram shows an example scenario where a device that runs enterprise software starts communicating over the Telnet protocol. Telnet activity is rarely associated with this software. Because Telnet is an insecure protocol that can enable an attacker to remotely control a device, this behavior should be investigated.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
