- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Domain controllers (DC) store valuable account data, making them a common target in post-compromise attacks. Remote Desktop Protocol (RDP) can help administrators connect to a DC and manage account data. But attackers with domain administrator credentials can also connect to DCs over RDP. If an attacker successfully establishes an RDP session with the DC, the attacker can update account information, steal passwords, and identify new targets in trusted domains.
The system might change the risk score for this detection.
Category
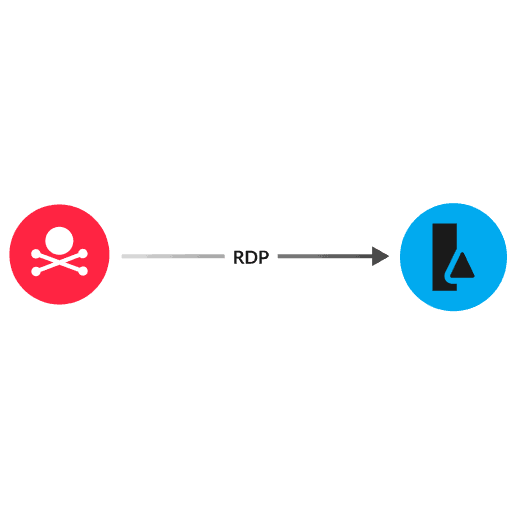
Active Directory provides a central point for managing account data in a network. The DC is a server that stores account data for a domain. Attackers who have infiltrated the network and acquired domain administrator credentials can remotely interact with a DC over RDP. The attacker sends an RDP request to the DC to open a connection. After an RDP session is established, the attacker interacts with account data on the DC through a graphical user interface (GUI).
Disable the Remote Desktop Service on devices unless required
Remove the default local Administrators group from the list of approved RDP groups and add specific users to the list
Only allow incoming external RDP connections from trusted devices
Limit the number of RDP login attempts, and then lock user accounts that exceed this number
Review access controls to ensure that only authorized users can connect through RDP
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
