- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
The Windows Print Spooler service runs on Windows domain controllers by default. Exploit code that injects malicious code into the Print Spooler service is publicly available, enabling an attacker to attempt to exploit the vulnerability to gain complete control of a device. Legitimate printer driver installations can appear similar to exploit attempts.
The system might change the risk score for this detection.
Category
Decryptions
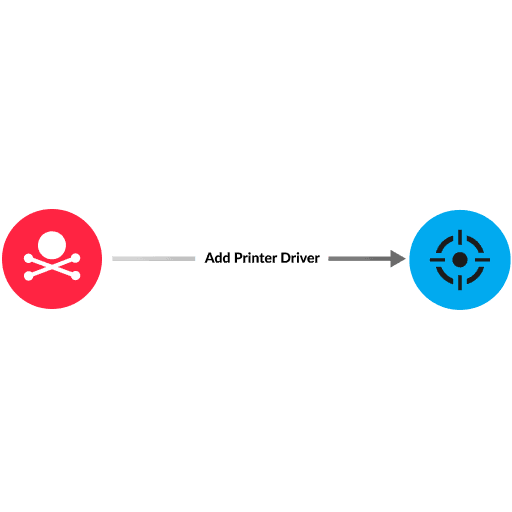
An attacker can create a malicious, unsigned printer driver DLL file and inject malicious, arbitrary code into the Windows Print Spooler service to perform remote code execution (RCE). An attacker makes remote procedure calls (RPCs) to RpcAddPrinterDriverEx(), RpcAsyncAddPrinterDriver, or RpcAddPrinterDriver, which are operations for remotely installing a printer driver file (such as a DLL file) on a system. The DLL file contains malicious code. In modern Microsoft environments, the operations and malicious DLL file name can be concealed from network defenders within an encrypted SMBv3 or RPC connection. After the Print Spooler service runs the malicious code with full SYSTEM privileges, the attacker is able to install malware, change data, or create new accounts with full user rights. PrintNightmare is an RCE vulnerability in the Print Spooler service that fails to restrict access to operations required to install a printer driver on a system remotely. Unless the server is vulnerable to PrintNightmare, the attacker must have correct privileges and policies on the server to remotely install a malicious unsigned printer driver.
Install patches for affected devices
If unable to patch, make the recommended changes provided in Microsoft Security Update Guide for CVE-2021-34527 (see the link below)
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
