- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Metasploit is a well known attack tool for generating exploit code and handling command-and-control (C&C) communication. Default settings in Metasploit facilitate attacks for less experienced or hasty attackers. Through a persistent command-and-control C&C channel, an attacker can remotely control a device and gain an entry point for further attacks on the network.
The system might change the risk score for this detection.
Category
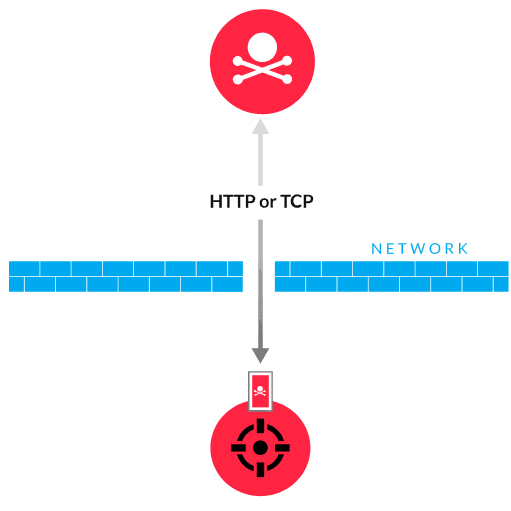
The Metasploit Framework includes several modules for generating payloads with exploit code. The most common payload type is the Meterpreter payload, which helps manage C&C channels. The Meterpreter payload is delivered to the victim through a successful exploit and the payload initiates a TCP or HTTP connection with a C&C server running the Metasploit module. A Meterpreter session is then opened, enabling the attacker to run commands on the victim.
Apply system updates regularly to reduce the number of vulnerabilities that can be exploited
Quarantine the client while checking for indicators of compromise
Block inbound and outbound traffic from suspicious hosts at the network perimeter
Implement network segmentation and the principle of least privilege on accounts to minimize the damage caused by a compromised device
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
