- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Attack tools that perform the Kerberoasting attack technique are publicly available and well known. An attacker with valid domain credentials and network access to a domain controller (DC) can request service tickets that contain ciphertext of service credentials. If the attacker successfully decrypts service tickets offline, they can recover credentials for a service account, which can lead to further attacks on your network.
Category
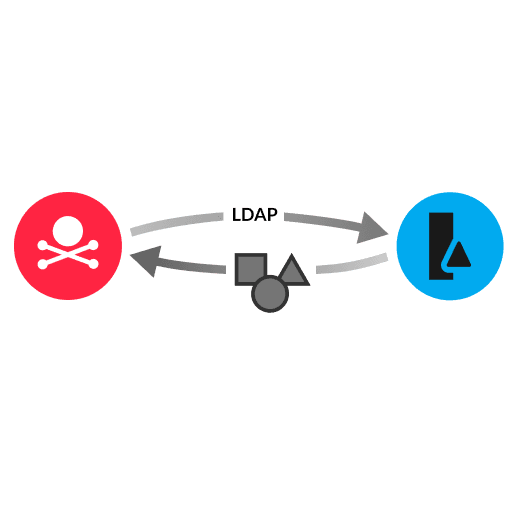
An attacker sends LDAP queries to identify targets-of-interest for theft of Kerberos tickets. The attacker targets service accounts for service tickets or user accounts (both user-level and admin-level). The service ticket contains ciphertext of service account credentials. After acquiring the service ticket, the attacker performs offline cracking of ciphertext to steal the credentials and impersonate other users or service accounts. User accounts are often more susceptible to password-cracking with Kerberoasting because of weak user-generated passwords.
Require LDAP signing, which prevents non-domain users from querying the LDAP server.
Implement LDAPS and proper Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC), and monitor and log LDAP activity.
For Kerberos implementations, disable the RC4 encryption type and enforce least privilege and complex passwords for service accounts (more than 25 characters). Apply automated password rotation solutions for managing service accounts and decommission unused service accounts.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
