- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
It is both relatively easy and common for attackers to gain access to network file shares to attempt data staging, which is the process of collecting and preparing data for exfiltration. Depending on the sensitivity of the files in the accessed file share, the impact can be devastating if important, proprietary, or customer data is leaked.
The system might change the risk score for this detection.
Category
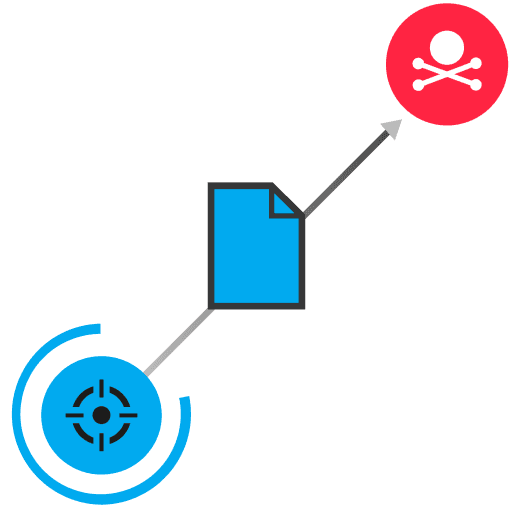
After an attacker has compromised a workstation and obtained credentials, they can proceed with malicious activity that might be overlooked as normal file share activity. The primary difference is that the attacker is looking for sensitive or valuable information that they can leverage for malicious objectives, such as in a data breach.
Disable FTP unless required
Restrict file share access to only authorized IP addresses and hosts
Disable anonymous authentication on FTP servers unless required
Track suspicious activity by implementing strict audit controls on important documents
Implement strict rules for outbound traffic on devices that contain valuable data
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
