- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Impacket is an open-source collection of tools for manipulating packets and network protocols such as SMB/CIFS. An attacker with local administrator privileges can run the SecretsDump tool to steal account names and cached credentials and move laterally across the network.
Category
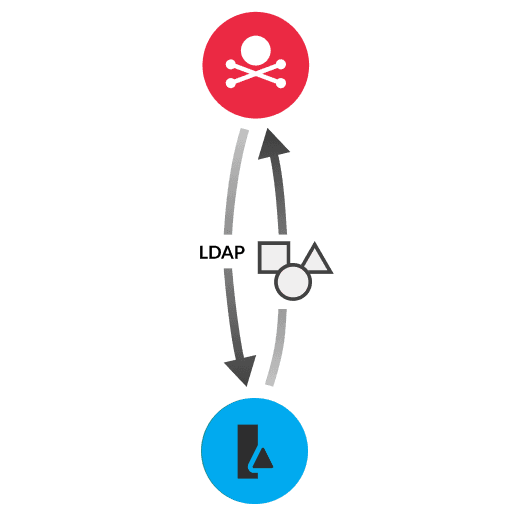
Impacket is a toolset that includes SecretsDump, a python script that can remotely retrieve cached credentials from the Security Account Manager (SAM) and Local Security Authority (LSA) Windows registry hives. SAM is a database file that stores local accounts for the host. LSA stores plaintext passwords and credentials, such as credentials for service accounts.
An attacker that has obtained local administrator privileges can run SecretsDump to access SAM and LSA. The script sends a Microsoft remote procedure call (MS-RPC) command to dump cached credentials from the Windows registry hive into a temporary file. The attacker can then read the temporary file over SMB to retrieve credentials.
Disable or restrict NTLM authentication
Limit the caching of plaintext credentials by adding users to the Protected Users Active Directory security group
Limit the number of cached credentials stored in the Windows registry (HKLM\SOFTWARE\Microsoft\Windows NT\Current Version\Winlogon\cachedlogonscountvalue)
Restrict file share access in Windows firewall settings to only authorized IP addresses
Do not allow remote access by users with local administrator credentials
Do not allow user or admin domain accounts in the local Administrator group
Require separate administrator credentials for different types of remote activity
Learn how attackers use the Impacket tool to move laterally in encrypted east-west traffic. Discover how ExtraHop RevealX provides the crucial visibility to detect these hidden threats.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
