- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
An attacker with network access and valid privileges can easily copy files to Windows autostart paths. This technique is uncommon because it is easily detected. However, if an attacker can successfully install a payload that is later run on the victim device, the attacker can establish persistence or laterally move across the network.
Category
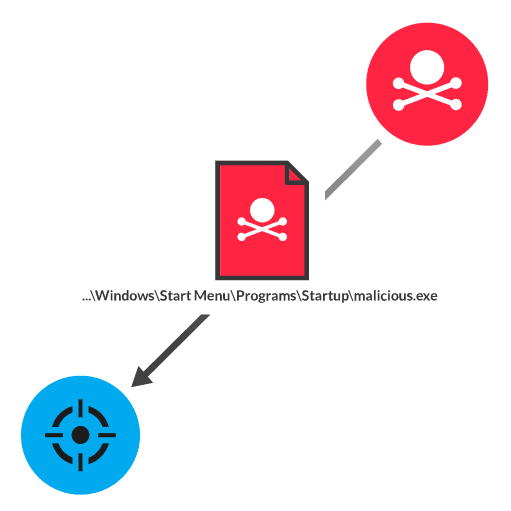
After infiltrating a network, an attacker can laterally move across the network by compromising new target devices. While an attacker can transfer an executable file to a target device over the SMB protocol to a Windows device, a malicious payload will not automatically run. However, an attacker with administrator credentials can copy the file to a startup path, such as C$\Users\Administrator\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup. The files in this path run automatically during startup processes, such as boot or login, delivering the malicious payload.
Quarantine the client while checking for indicators of compromise
Disable SMB file sharing unless required
Apply the principle of least privilege to permissions for modifying autostart paths
Implement network segmentation, security zones, and firewall policies that limit how devices can communicate
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
