- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Citrix NetScaler devices are exposed to the internet and the code that exploits this vulnerability is publicly available. An unauthenticated attacker can attempt to steal session tokens from a server that has unpatched versions.
Category
Decryptions
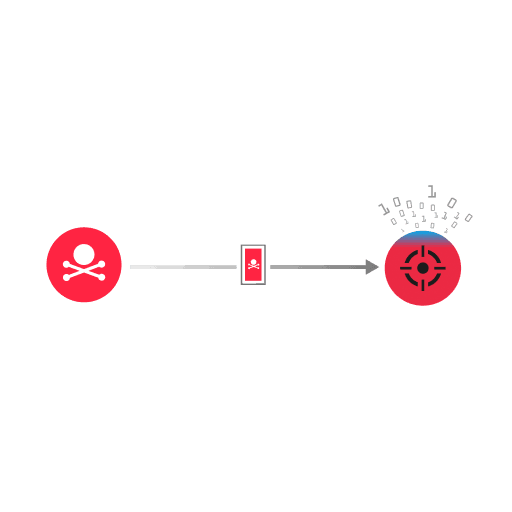
Citrix NetScaler Application Delivery Controller (ADC) and NetScaler Gateway have a sensitive information disclosure vulnerability. An unauthenticated attacker can take advantage of this vulnerability by sending an HTTP request with a large amount of data (>21739 bytes) in the Host header. The victim processes the request, which results in a buffer overread. The memory beyond this buffer contains a global structure that can include a session token. When the victim sends a response with a non-200 status code or without a session token, the exploit attempt is unsuccessful.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
