- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
An attacker with network access to a vulnerable device can leverage public exploit code or attack tools to access server data. Depending on the data accessed, the impact can be significant if important data is stolen, modified, or deleted.
Category
Decryptions
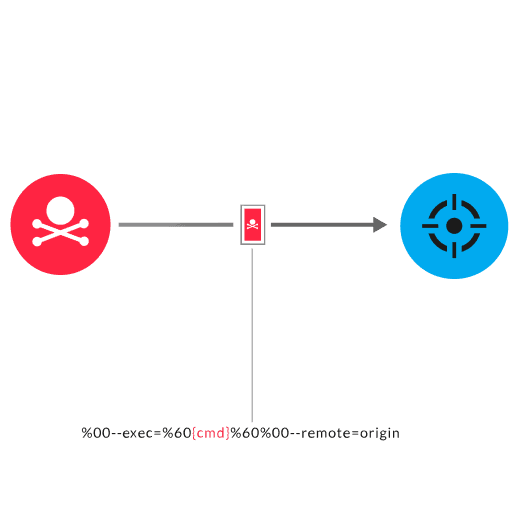
Atlassian Bitbucket is a Git management tool that enables users to create repositories to store files. Bitbucket has a vulnerability in how it sanitizes HTTP requests with null bytes, which enables command injection. An unauthenticated user with read access to a public repository or an authenticated user with read access to a private repository can exploit this vulnerability to run shell commands on the Atlassian server. The attacker sends a malicious HTTP request with URL-encoded null bytes (%00) followed by an argument (--exec), command, and null bytes followed by an argument (--remote).
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
