- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Serv-U servers are often exposed to the internet. This vulnerability is well known and actively exploited. An unauthenticated attacker can gain complete control of a device.
Category
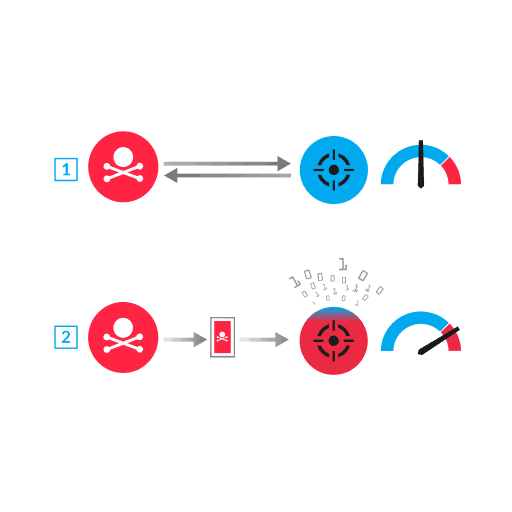
SolarWinds Serv-U has two file server products for sending and receiving files over multiple protocols: Serv-U File Transfer Protocol (FTP) and Serv-U Managed File Transfer (MFT). These products for Windows have a remote memory escape vulnerability when specific options are enabled, such as SSH File Transfer Protocol (SFTP). This vulnerability is exploited in three steps. First, the attacker connects to an open SSH port on the Serv-U server and sends multiple SSH messages without completing the SSH handshake. The messages insert malicious payloads into the Serv-U process memory. Next, the attacker exploits the vulnerability by sending disordered SSH handshake messages that skip a key exchange and specify the AES128-CTR encryption protocol (1). As a result of not having the keys, the Serv-U server is unable to decrypt a malicious encrypted packet sent by the attacker, which causes malicious payloads in the Serv-U process memory to run as a Windows service with SYSTEM privileges (2).
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
