- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
This vCenter plugin vulnerability is well known and requires network access to port 443 on a vCenter server. An unauthenticated attacker can leverage public exploit code to gain complete control of a device or escalate privileges to spread malware, such as ransomware, across the network.
Category
Decryptions
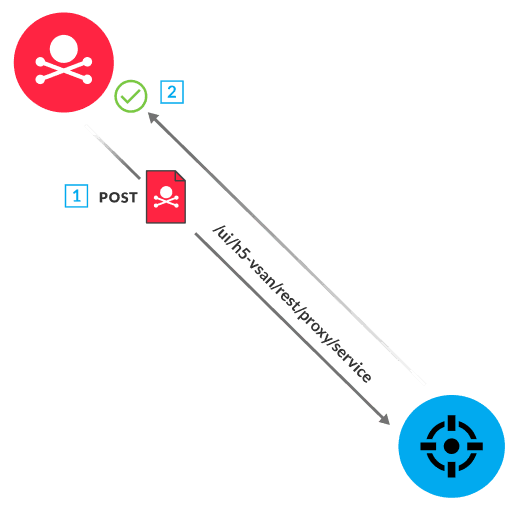
The VMware vSphere Client (HTML5) component of VMware vCenter enables the management of virtual environments for Windows and Linux hosts. vCenter has default plugins that monitor vSphere Client connections. A vulnerability in the Virtual SAN Health Check plugin (which is enabled by default) allows an unauthenticated attacker to successfully access classes and methods from a vulnerable endpoint (/ui/h5-vsan/rest/proxy/service) on port 443. The attacker can leverage vulnerable endpoints to look up a malicious class on the victim server, resulting in remote code execution (RCE) on the vCenter server through Java Naming and Directory Interface (JNDI) injection.
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
