- Platform
- Solutions
- Modern NDR
- Resources
- Company
Platform
Modern NDR
Resources
Company
DETECTION OVERVIEW
Risk Factors
Cryptocurrency mining software is easy to install; only a small amount of code and a cryptocurrency wallet address are needed to convert stolen resources into profit. Attackers commonly install cryptocurrency mining software on a large number of machines to aggregate more resources into a cryptocurrency mining pool and collect more cryptocurrency. Cryptocurrency mining does not typically involve destroying or stealing data. However, the continuous high CPU, GPU, or ASIC usage on victim computers can cause performance degradation. Unauthorized software on a workstation can also introduce vulnerabilities, backdoors, or hidden malware into the network.
Category
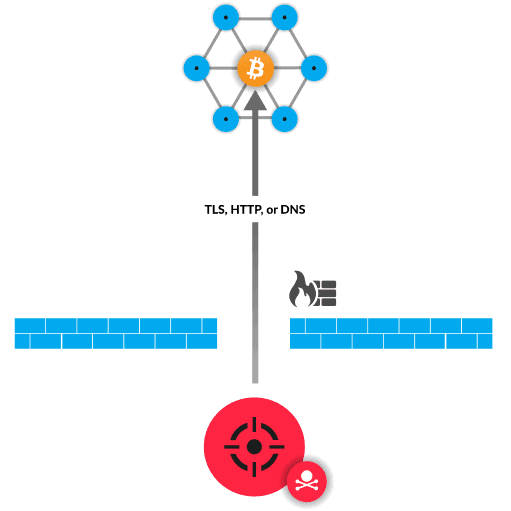
Cryptocurrency mining is the process of converting computing resources into cryptocurrency. The process is costly in terms of electricity, time, and processing power. A cryptocurrency mining pool allows users to aggregate computing resources. Each user then shares the cryptocurrency awards based on their contribution. A malicious crypto miner might steal resources to offset costs, increase their contribution, and maximize profit. For example, an attacker can hijack resources from unsuspecting victims by installing cryptocurrency mining malware on victim machines.
Add firewall rules to prevent traffic over known cryptocurrency mining software ports
Block domain names for known mining pools
Implement controls that prevent unauthorized applications from running on host and virtual machines
Implement strong IT policies to prevent unauthorized host and virtual machines from running cryptocurrency mining software
Network analysis and visibility solutions remain underrepresented in enterprises. Find out why in this preview of a new Wave report.
ExtraHop® Named a Leader in First-Ever Gartner® Magic Quadrant™ for Network Detection and Response
Visit this resource for more information.
This analysis exposes the critical link between an organization's lack of internal visibility and the escalating cost of compromise, demanding an urgent re-evaluation of how core business assets are protected.
Learn why you need to be wary of the claims certain network detection and response providers make about their coverage against the MITRE ATT&CK framework.
Learn how NDR from RevealX helps security teams detect and investigate more adversary TTPs in the MITRE ATT&CK framework than rule-based tools.
