 Blog
Blog
How to Detect and Respond to the SUNBURST Attack
ExtraHop
December 14, 2020
See Part 2: Analyzing the SolarWinds Orion SUNBURST Attack Campaign For Threat Intelligence
The SUNBURST backdoor, disclosed on December 13th, is a supply chain attack involving a trojanized update to the popular SolarWinds Orion IT monitoring and management suite. The backdoor affects servers running the Orion software, which are often less defended than end-user laptops or critical applications. Given the resources and sophistication of these threat actors, including the use of supply chain attacks against infrastructure and workloads, traditional defenses are ineffective and organizations should prioritize network detection. Because the network is as close to ground truth as you can get, difficult to evade, and impossible to turn off, sophisticated analysis of network data offers the best opportunity to detect, investigate, and respond to these threats before a breach can occur.
According to ExtraHop's data, the attack appears to have been underway for some time. The ExtraHop analysis of DNS registration information indicates that the SUNBURST attack campaign can be traced back to February 26th, 2020. This appears to be when the command and control (C&C) domain name avsvmcloud[.]com was first registered, and the site went active on April 15th, 2020.
“Nation-states have means of stealing information through traditional espionage. They could bribe or extort company employees or even place operatives within the organization. The reason we are seeing an uptick in sophisticated cyber attacks is geopolitical. That is, for better or worse, it's accepted that nation-states can operate in the cyber theater with relative impunity. Until this changes, companies should expect more of these operations.”
Jesse Rothstein, CTO and Co-founder, ExtraHop
The SUNBURST Vulnerability and Network Detection and Response
The Cybersecurity and Infrastructure Security Administration (CISA) has issued Emergency Directive 21-01, with the various investigation and mitigation requirements, including ordering all federal agencies to immediately disconnect affected products. In a statement, CISA said, "We urge all our partners—in the public & private sectors—to assess their exposure to this compromise and to secure their networks."
This supply chain attack has reportedly compromised communications of the US Treasury and Commerce Departments. According to Krebs on Security, the potential impact to Fortune 500 companies, telecommunications, government, and universities is wide-reaching. SolarWinds themselves have issued a security advisory recommending their customers upgrade to Orion Platform version 2020.2.1 HF 2 as soon as possible.
NOTE: Microsoft labeled the attack "Solorigate" in Windows Defender. FireEye refers to the backdoor as SUNBURST, which is the naming convention that ExtraHop will use as well. The attackers behind this campaign are being tracked as UNC2452.
ExtraHop believes this attack will have wide-reaching implications and has outlined steps our customers should take to detect and mitigate this threat. ExtraHop Reveal(x) network detection and response is uniquely positioned to mitigate the risk created by the SUNBURST trojan. Reveal(x) is always on and always analyzing. The system records extensive historical metadata and metrics, which can be queried to hunt for specific threats. Here are some steps you can take to detect instances of the malware with Reveal(x).
How to Hunt for, Detect, and Respond to SUNBURST with ExtraHop Reveal(x)
Look for Command-and-Control Detections
Because Reveal(x) uses a spectrum of detection approaches, SUNBURST's behavior can trigger multiple distinct detectors such as behavioral command-and-control detectors that identify persistent, beacon-shaped web traffic to uncommon external destinations. As such it is recommended that analysts pay close attention to any command-and-control detections surfaced by Reveal(x).
NOTE: The ExtraHop Threat Research team is in-process confirming that the existing Reveal(x) beaconing detector will catch communications from this particular trojan. Additional details will become available over the next few days.
How to Hunt for SUNBURST with ExtraHop Reveal(x) Records
While current and future detections are important, looking backward to find any existing C&C communication records is vital to ensuring that all attackers are eliminated. The first step is to look for the C&C domain names used by the trojan, like avsvmcloud[.]com.
To do this, navigate to "Records" and select the "Record Type" drop-down. Choose "DNS Requests," then change the "Any Field" drop down to "Query Name" and search for "avsvmcloud" or any of the other domain names below.
There are currently twelve domains that appear to have taken part in the attack. ExtraHop recommends searching for the following domains. Any interactions with these domains could indicate that you have been compromised by the SUNBURST backdoor. This list might be updated in the future.
The domains are as follows:
- avsvmcloud[.]com
- incomeupdate[.]com
- zupertech[.]com
- databasegalore[.]com
- panhardware[.]com
- digitalcollege[.]org
- freescanonline[.]com
- deftsecurity[.]com
- thedoccloud[.]com
- virtualdataserver[.]com
- websitetheme[.]com
- highdatabase[.]com
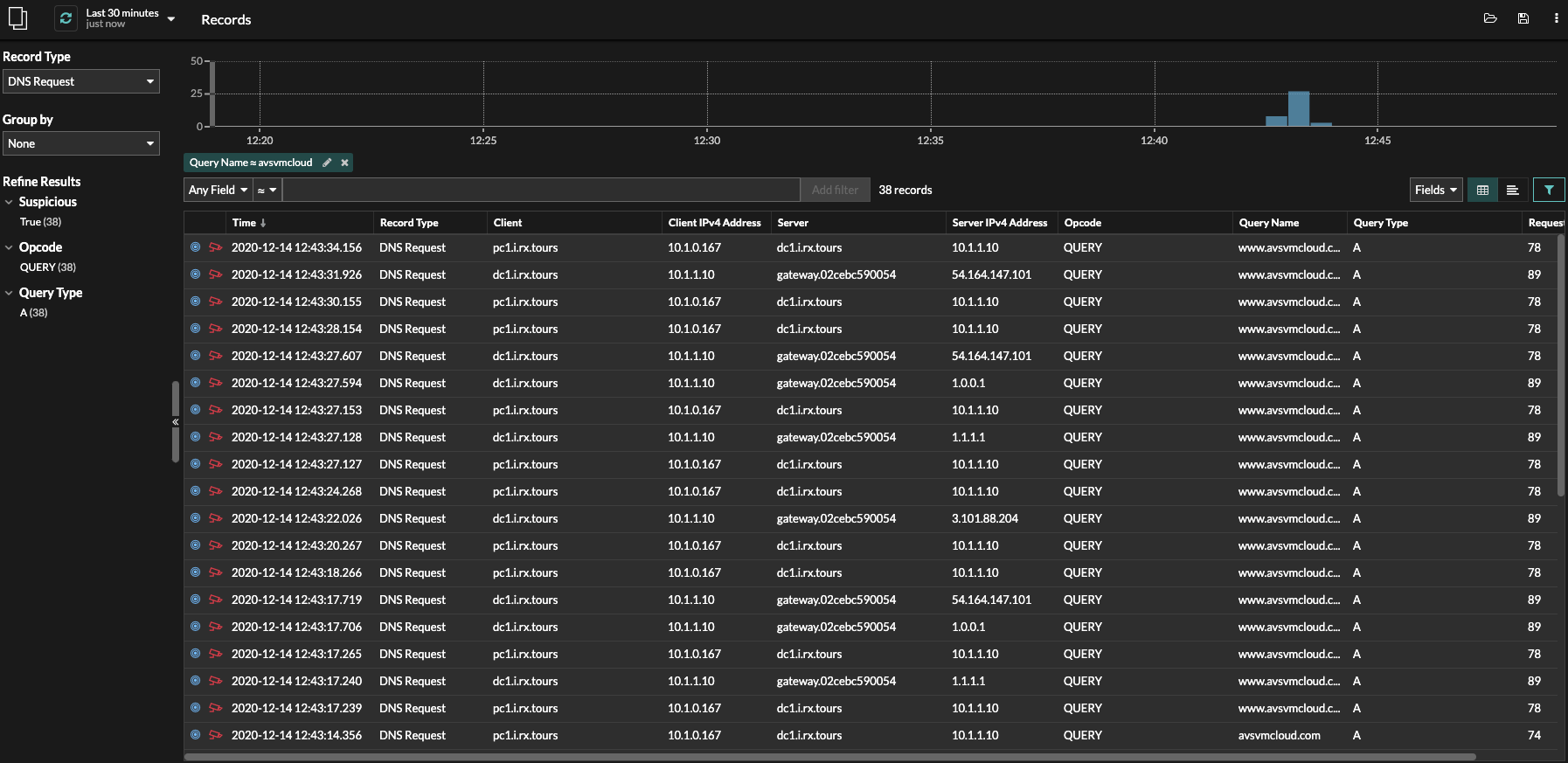
Reveal(x) records search showing IOC results.
Next, change your date criteria in the upper left-hand corner to go back as far as you like. Any recent queries will show as suspicious with a red camera icon. Searches of older records before December 14th will surface any matching domains if present in that timeframe, but will not show the red camera icon indicating a suspicious domain before the threat intelligence (TI) feed was updated to include the domain names.
NOTE: Reveal(x) 360 SaaS customers automatically have 90 days of record lookback to search. On-premises deployments might have less lookback depending on the record volume.
It will be helpful to group these by the client to get a list of unique hosts that need to be patched. To do this, select the dropdown below "Group By" and choose "Client" from the list.
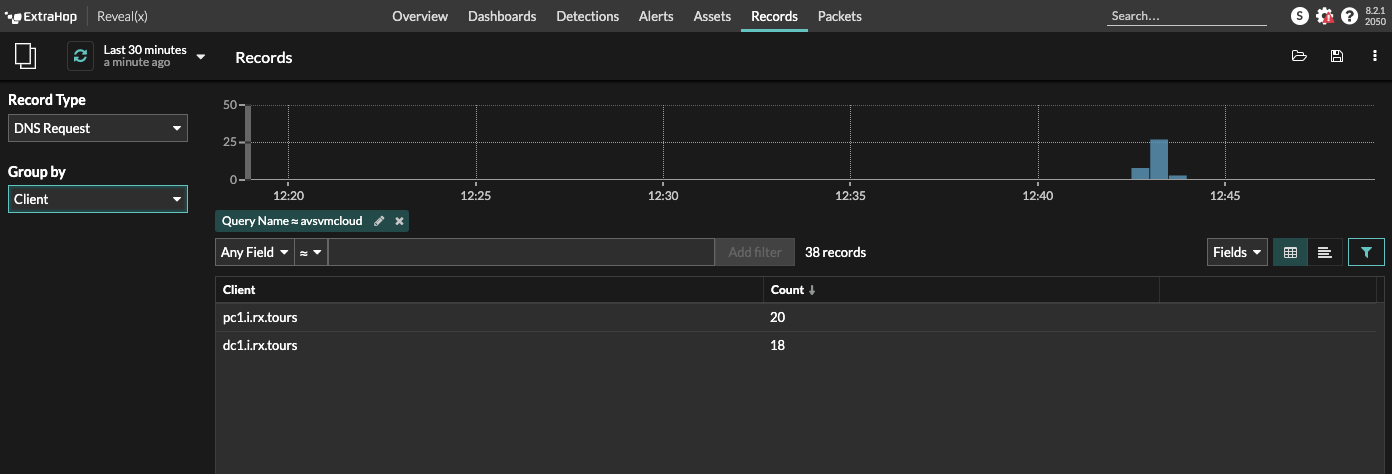
Reveal(x) records dashboard grouped by client.
Any devices using these domain names are likely infected and should be patched as soon as possible. DNS servers will likely show up in these searches as they are forwarding requests for afflicted devices.
Pro tip: Be sure to save this query for future reference using the save icon at the top right of your Records screen.
How to Hunt for SolarWinds in the Environment
To determine if SolarWinds products are installed in your environment, perform a record search as outlined above for the following domains:
- licenseserver.solarwinds[.]com
- licensestatusserver.solarwinds[.]com
- api.solarwinds[.]com
- installer.solarwinds[.]com
- updates.solarwinds[.]com
If communications with these domains are discovered in your environment, it is highly advisable to identify which SolarWinds products are installed to determine if you are susceptible to the SUNBURST trojan.
How to Hunt for SUNBURST with ExtraHop Reveal(x) Metrics
If records are not available, metrics can be checked for the C&C domain names used by the trojan, like avsvmcloud[.]com. We recommend that ExtraHop users run the script in the following directory (sunburst) through the REST API.
For more information, reach out to your ExtraHop Sales Engineer.
ExtraHop: Building Detections for Immediate Response
ExtraHop Reveal(x) is constantly enhanced to allow for rapid delivery of new, high-fidelity detectors on emerging threats. These capabilities are further enhanced by the Reveal(x) 360 platform, which allows for record stores with 90 days worth of historical data—giving analysts what they need to perform threat investigations.
ExtraHop has created a detection specifically for this issue.
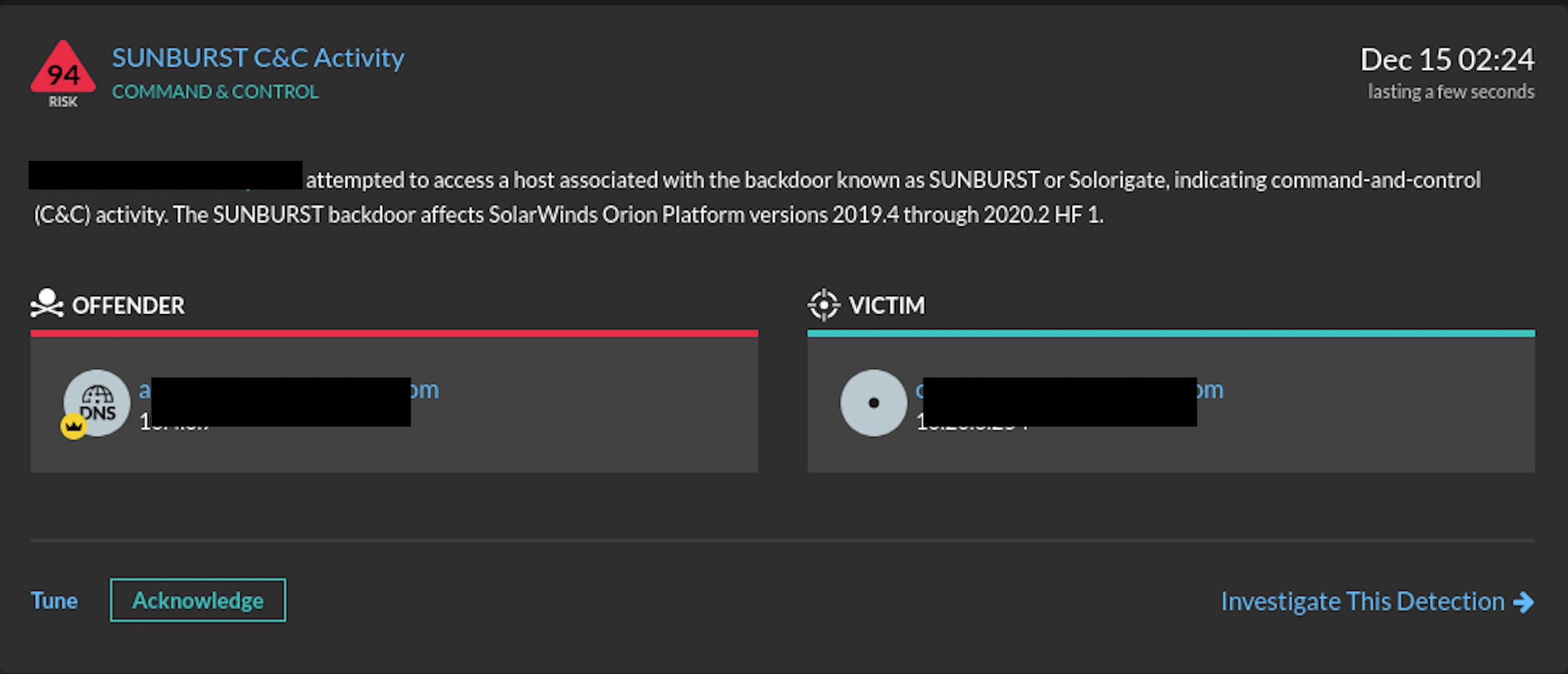
Reveal(x) detector for SUNBURST.
ExtraHop is committed to staying on top of important events that affect our customer community. If you have any questions please reach out to your regional or customer support representative.
Watch these videos for more:
Further Information
Find DNS Queries to SUNBURST C&C Domains
We recommend that ExtraHop users run the script in the following directory (sunburst) through the REST API.
SUNBURST Domains
- incomeupdate[.]com
- zupertech[.]com
- databasegalore[.]com
- panhardware[.]com
- avsvmcloud[.]com
- digitalcollege[.]org
- freescanonline[.]com
- deftsecurity[.]com
- thedoccloud[.]com
- virtualdataserver[.]com
SUNBURST Strings:
"<p>Million-Support-Years-Week-Agents</p>" "<title>Woman-Five-How-To-Why-Your-Celebrating-Learn-Brand</title>" "<p>Companies-Best-Man-Vendors-Best</p>" "/swip/Events HTTP/1" [when not sent to .solarwinds.com] "/swip/upd/SolarWinds.CortexPlugin.Components.xml" [when not sent to .solarwinds.com] "swip/Upload.ashx HTTP/1" [when not sent to .solarwinds.com] "/swip/upd/" [when not sent to .solarwinds.com] "<meta name="msvalidate.01" content="ECEE9516DDABFC7CCBBF1EACC04CAC20">" "<meta name="google-site-verification" content="CD5EF1FCB54FE29C838ABCBBE0FA57AE">"
Sources:
- https://github.com/fireeye/sunburst_countermeasures
- https://msrc-blog.microsoft.com/2020/12/13/customer-guidance-on-recent-nation-state-cyber-attacks/
- https://www.fireeye.com/blog/threat-research/2020/12/evasive-attacker-leverages-solarwinds-supply-chain-compromises-with-sunburst-backdoor.html
- https://isc.sans.edu/diary/rss/26884
Updated: December 16, 2020